Why identity management in the digital workspace is essential for organisations?
Workplace mobility allows employees to connect to almost any network wherever they are to work. While this gives them the flexibility to work wherever and whenever they want, it sometimes can create another problem for companies. IT departments are finding it harder to keep track of who accesses company data using third party devices or sources. Not only does this create a security vulnerability for organisations, but it also means companies would need to spend more time to check who is accessing them and if these devices pose a threat to the organisation.
At the same time, it is estimated that there will be around 75.4 billion IoT devices by the year 2025. From personal mobile devices to smart printers in offices, the growth of IoT devices, especially in the workplace, will not only change the way we work but the way we view cybersecurity as a whole. With employees preferring to use their own devices for work these days, organisations are now finding it harder to track the amount of data that’s being transferred by these devices.
This absence of control and visibility over IoT devices and access have led to breaches in organisations before. A recent example would be the data breach suffered by Malindo Airlines in 2019. According to the airline company, two former employees of an e-commerce services provider in India had improperly accessed and stole the personal data of the airlines’ customers. A huge number of accounts were exposed, leading to the airline requesting customers to reset their account passwords.
By the time the airline realised about the breach, it was too late. Information such as passport details, home addresses and phone numbers were leaked onto data exchange forums on the dark web.
Malindo Airlines was not the only airline to suffer such a breach though. In 2018, the personal data of 9.4 million passengers from Cathay Pacific Airways and Hong Kong Dragon Airlines were leaked as well. The airline had said the breach was caused by unauthorised access to some of the passenger data is managed. Compromised data included passenger details such as nationalities, emails, passport and identity card numbers.
Now, if the airlines had visibility over who was accessing their data at that point of time, the breaches may have been able to be contained and the damage would not be as huge as this. They would have been alerted about the unauthorised access to their data and could have taken prompt actions to stop it.
At the same time, companies also need to be able to remotely grant and deny access to employees leaving or joining the organisation. In the Malindo Airlines case, the airlines should have immediately removed the access of the former employees of that particular company the moment they were no longer needed.
It’s not just about controlling access. Employees using their own devices for work may also compromise companies. Newer technologies bring in newer and more advanced devices. But not many of these devices, especially personal ones, are patched with cybersecurity protection when they are used for work. The digital workspace is fast becoming the norm for the modern workspace which is why organisations need to ensure their employees are accessing their work with secured devices.
This is where VMware’s Workspace ONE comes in. VMware Workspace ONE is a management platform which allows IT administrators to have control over access for end-users’ mobile devices as well as cloud-hosted virtual desktops. This also includes applications from the cloud or from an on-premises deployment. Meaning, breaches like the one experienced by Malindo Airlines can be avoided as IT administrators can remotely lockout users that no longer need access to the company.
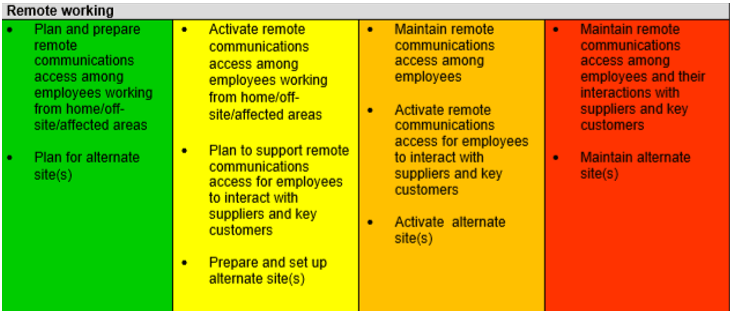
Apart from that, more employees today prefer working out of the office due to the nature of their job. Companies give them this flexibility as long they produce results. Recently though, circumstances are making employees having no choice but to work from home.
The recent Coronavirus outbreak has indeed caused some problems to the workforce as employees find themselves being confined and quarantined to their homes. Those that are sick are being taken cared of, but for the rest, they’re just eager to get back to work, but circumstances don’t allow it. So, they have no choice but to use their own devices and work from home.
This is where the security features of Workspace ONE makes it the ideal platform to monitor employee devices. Having employees work from home is one thing, but companies need to ensure the devices they use for their work are well secured and protected. Often times, employees would use their personal devices when working from home. Personal devices may not have the necessary security protection needed when accessing sensitive work documents. Also, the network they are working on at home may not be as secured as an office network.
VMware Workspace ONE is the answer to what organisations need to ensure their employees have a secure digital workspace. The added visibility over the usage and access for IoT devices can help organisations reduce security threats. IT administrators are able to deliver applications and manage them fast, securely and cost-efficiently. To find out more about how your organisation can have control and visibility over your employee’s mobile devices through VMware Workspace ONE, click here.
*DISCLAIMER: This article was supported by Net One Asia. Net One Asia specialises in helping enterprises adopt remote-work culture, enabling staff to stay productive with a digital workspace environment.